Recruitment Automation Platform
Finally, a complete recruitment automation that provides powerful technology
for everyone involved in recruiting.
Accentuate your style with our exclusive
Cartier Replica, where
elegance meets exceptional craftsmanship. Experience the modern sophistication
of our AP Replica,
a symbol of avant-garde horology. Capture the spirit of adventure with our
iconic Rolex Watch Fake,
designed for those who dare to stand out.
Trusted by 120+ companies across
15 major industries
TurboHire is globally compliant with case studies across major industries like IT, Manufacturing, BFSI, Pharma amongst many more. Further the product is being used by Large Enterprises, Mid-market companies and fast growing startups
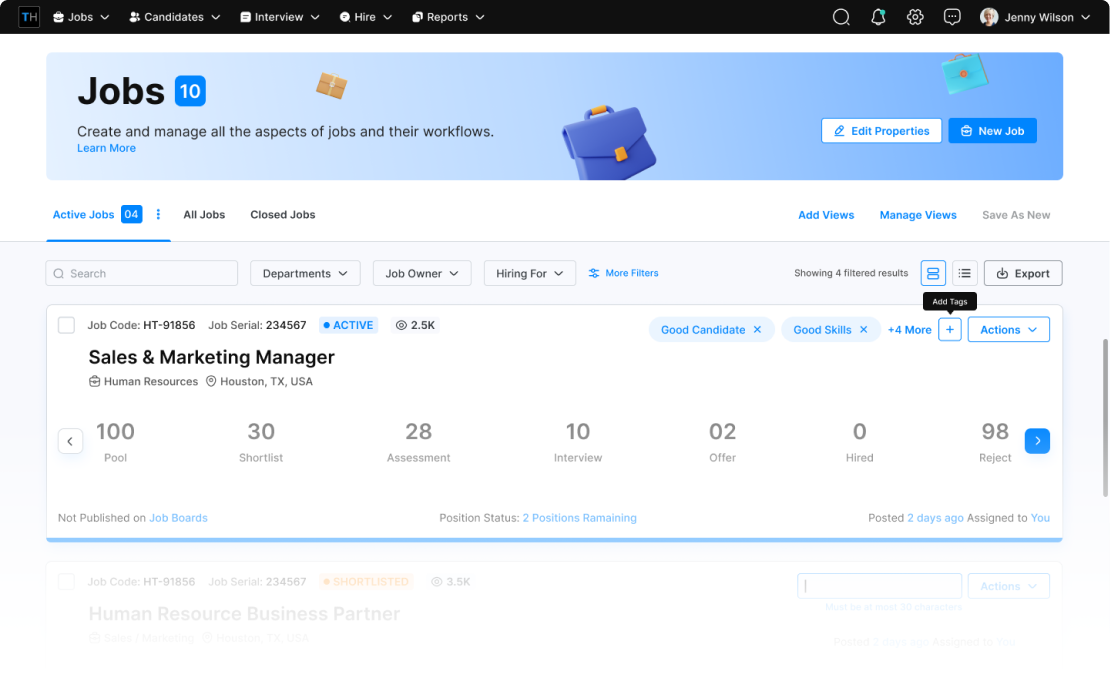
A Complete Recruitment Automation
Platform For Enterprises
Combining the power of 6+ types of recruiting product – truly all-in-one
TurboHire Platform
- At the core, TurboHire creates a single repository of resume and job data. Around this data, it provides 5 automation modules for sourcing, screening, engagement, interview, and offer. This leads to the automation of 85% of manual recruiting activities.
- The analytics layer encompasses all activities of all stakeholders to provide increased visibility into the recruitment process.


“The impact of TurboHire can’t be told it can only be experienced. I don’t know how we lived without TurboHire before”
Uma Maheshwari
Head Innovation & Talent Management
Enterprise(> 1000 emp.), Healthcare
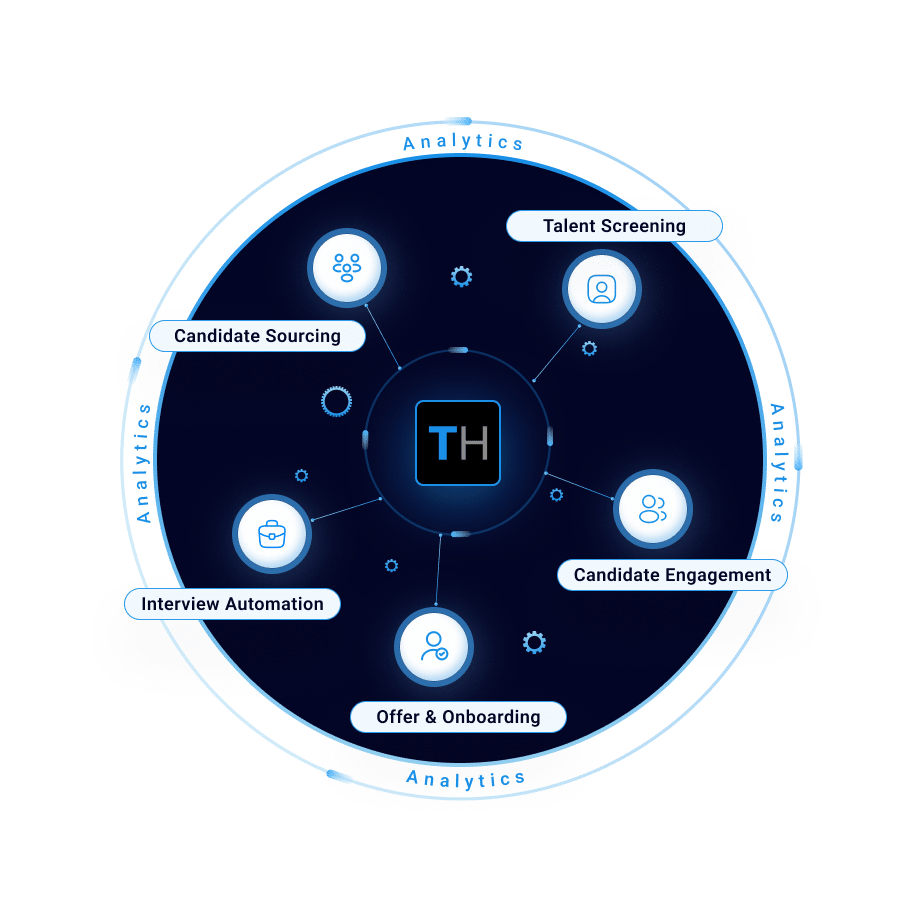
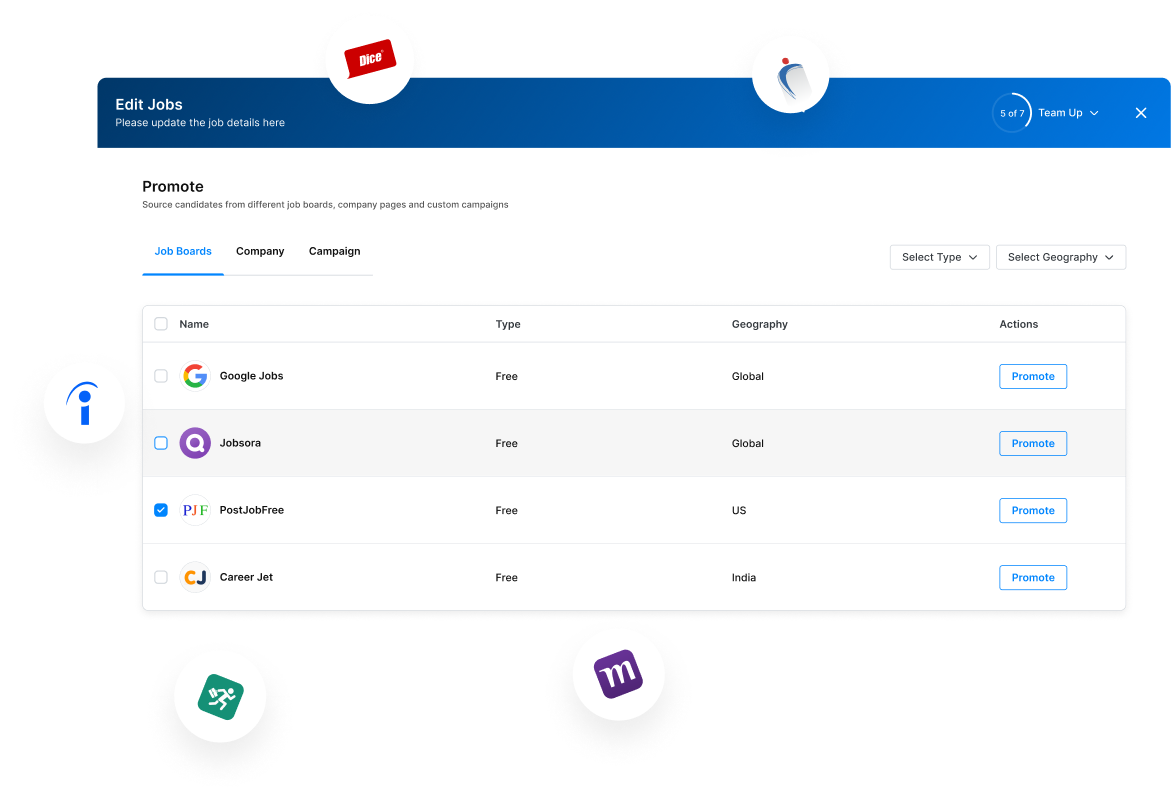
Candidate Sourcing
- TurboHire helps in sourcing new candidates from various job boards. It also makes sourcing from vendors easy with automated permission management and audit tracking.
- For passive sourcing, recruiting teams are empowered to reach out to candidates in their internal database or set up nurture campaigns to candidates from sources like LinkedIn for hard-to-fill roles.

“Turbohire reduces our dependency on a single candidate source and helps us source candidates 3X faster. The duplicate tracking and source mapping is a massive help”
Poonam S.
HR Manager
Mid-Market(51-1000 emp.), Education
Talent Screening
- TurboHire makes it easier to find the right candidate by parsing every resume into smart cards that enables filtering based on years of experience, previous roles or skills, etc. Further, it tags every candidate with an AI-generated score that automatically brings the best candidates toward the top of the stack.
- It helps in getting approvals from hiring managers on shortlisted candidates and makes it easier to conduct pre-screening assessments.

“The AI was helpful to reduce the manual effort in screening candidates by over 8 times. And my hiring managers love it when they can simply give feedback on candidates”
Veena J.
Lead Recruiter
Mid-Market(51-1000 emp.), Telecommunications
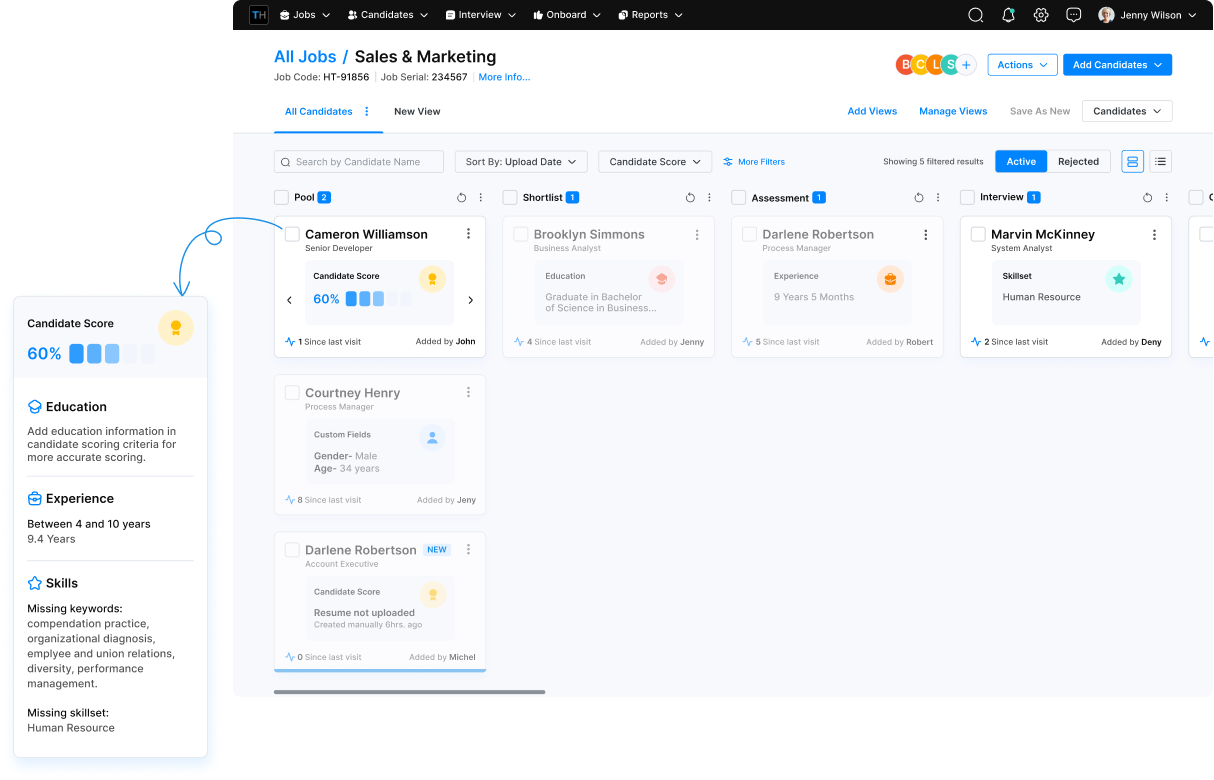
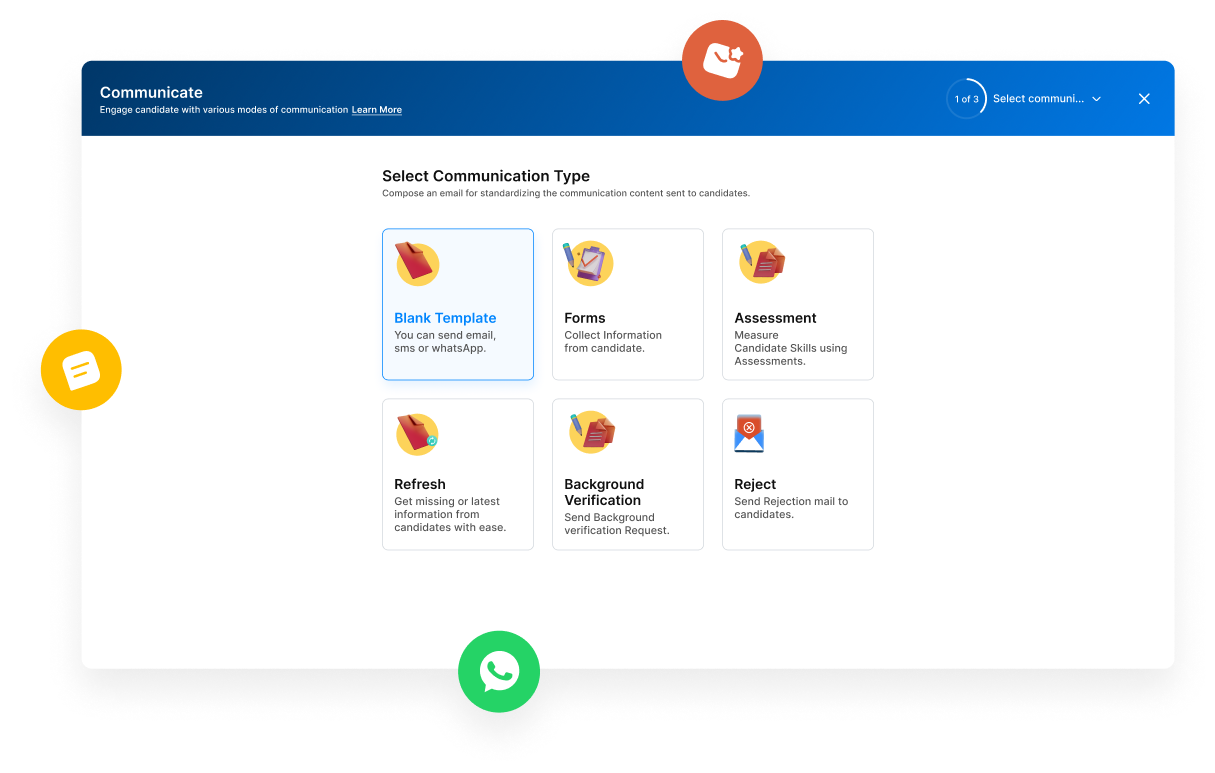
Candidate Engagement
- TurboHire allows templatized communications to candidates in bulk through emails. Further, it amplifies communication over SMS and WhatsApp resulting in quick response rates.
- It helps in structured data collection from candidates through forms. Candidates are allowed to submit video responses to express themselves better for the job.


“Our biggest delay in recruiting was a slow response from candidates. Using the multi-channel approach, we are seeing a 50% reduction in response time”
Himanshu S.
HR Generalist
Mid-Market(51-1000 emp.)
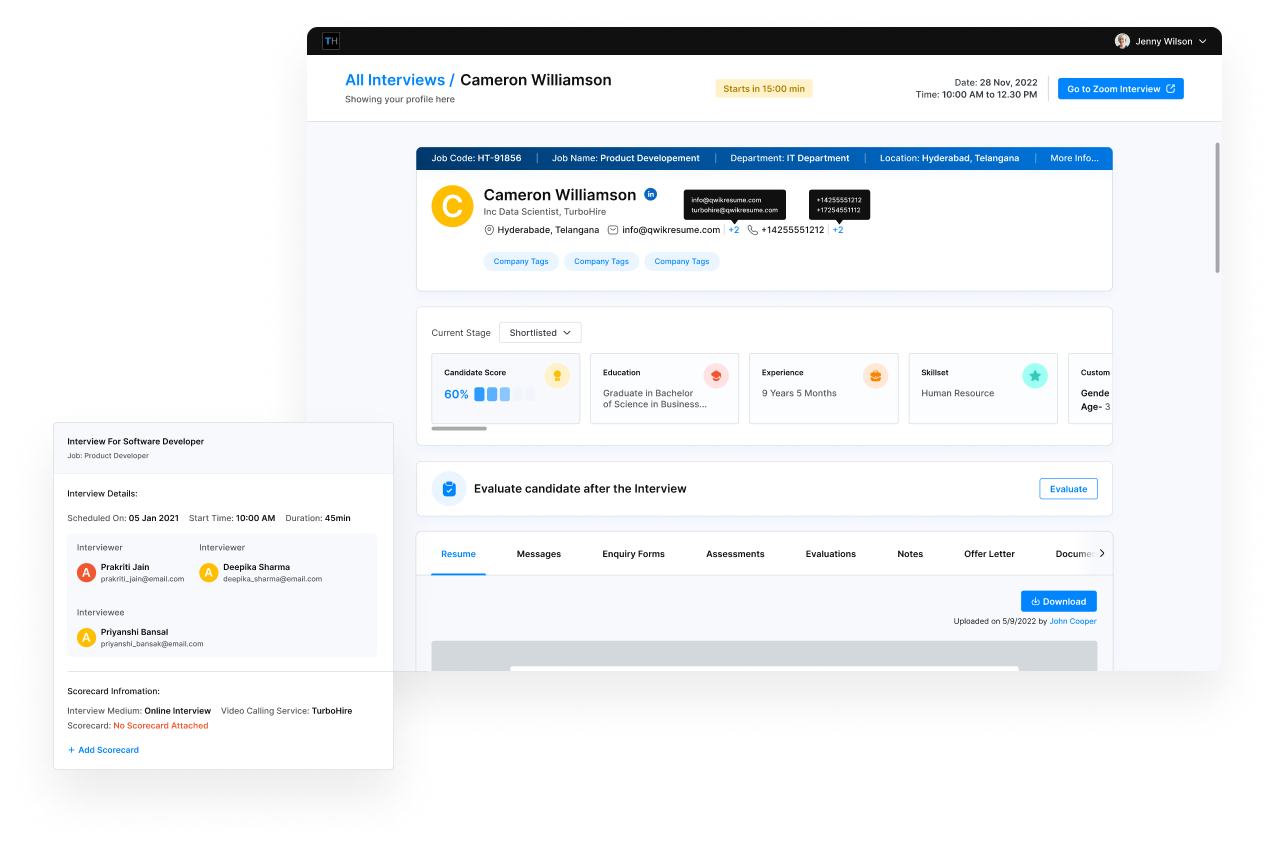
Interview Automation
- TurboHire enables effective interview scheduling by highlighting the free time slots of interviewers. It further provides an automated scheduling mechanism that helps broking time between candidates and interviewers.
- During interviews, it helps interviewers understand the candidate profile and previous evaluations while enabling them to leave feedback post-interviews in a structured manner.


“We are able to measure the number of interview schedules and cancellations using TurboHire. The auto-schedule feature is simply wow”
Yohanna F.
Manager for Talent Acquisition and Development (CoE)
Mid-Market(51-1000 emp.), IT Services
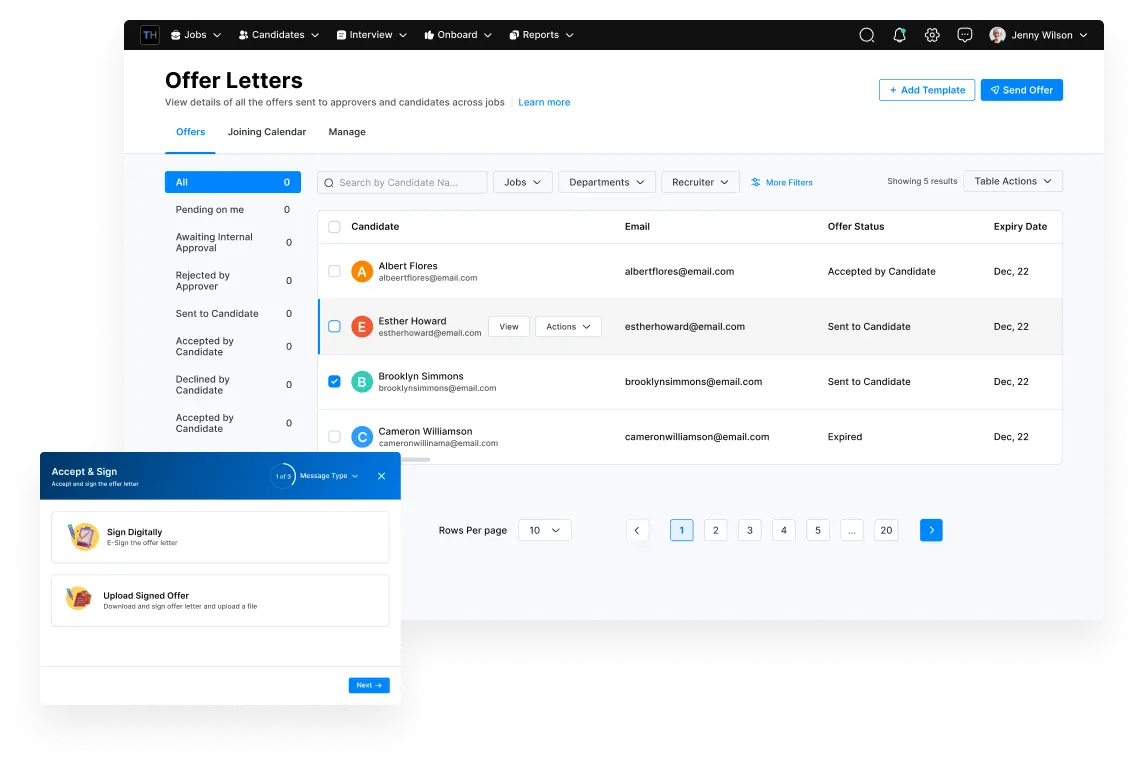
Offer & Onboarding
- TurboHire helps improve the offer process with the offer letter builder. It allows easy salary calculations through automated formulas.
- It provides a customizable approval workflow for internal approvals and digital signatures on the offer letters.
- It further allows the collection of important documents required for candidate onboarding and enables candidate engagement post-offer.


“We have multiple offer templates implemented in TurboHire and it helps us significantly in releasing offer letters. The bulk offer release feature is very helpful for college hires”
Amit M.
Senior Manager – Talent Acquisition
Enterprise(> 1000 emp.), ITES
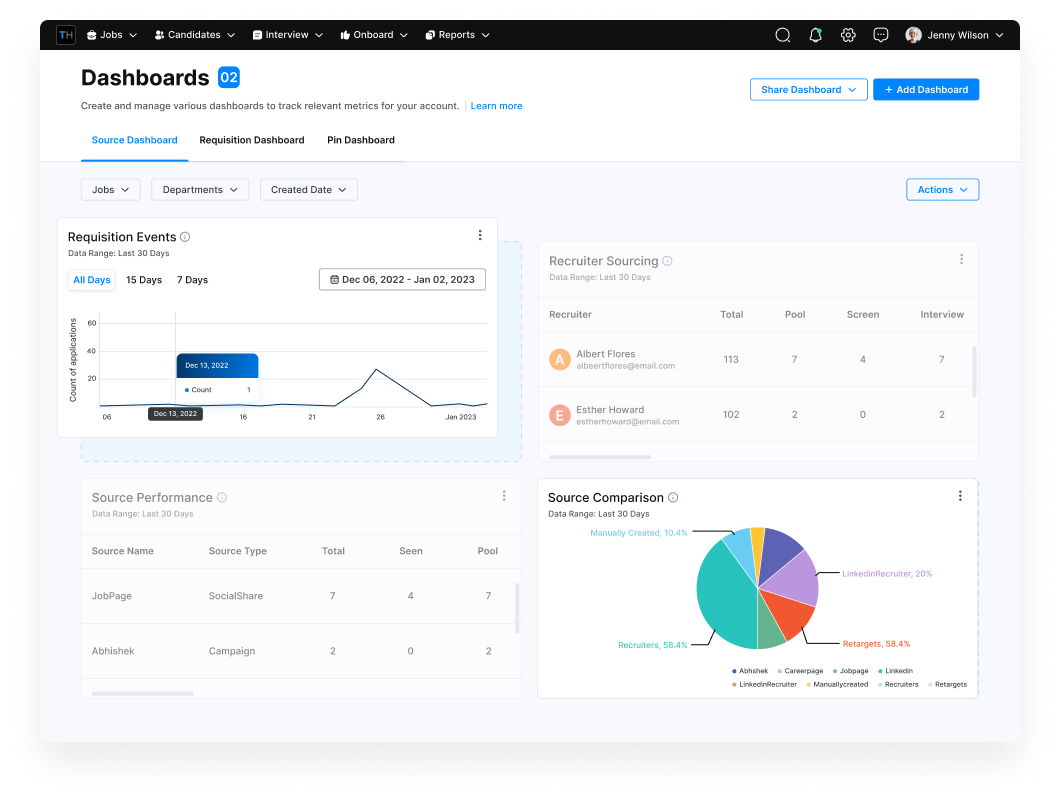
Recruitment Analytics
- TurboHire tracks every activity of every stakeholder involved in recruiting. This enables organizations to manage the audit trail of various different activities.
- It provides a robust reporting library out of the box. Further, the custom report builder enables organizations to build advanced reports. Finally, the reports can be viewed together in a form of an interactive dashboard.

“We use analytics extensively in TurboHire. It has not just helped us gain new insights but also helped improve collaboration with the business team who can now have an overview of the entire process”
Amey Y.
Associate-Human Possibilities- Repos Energy
Mid-Market(51-1000 emp.)
One Platform, Many Solutions
TurboHire is not a tool but a collection of tools (a toolkit)
built to solve your recruiting challenges.

HCM Add-on
Give the power of Intelligence & Automation to your HRMS platform with deep integrations with leading providers like SAP, Oracle.

Graduate Recruiting
Set-up an optimized campus hiring process to process large volume of candidate applications, process interviews and release offer letter at scale.

Careers Page
Bring AI to your careers page to improve candidate experience and get more inbound applicants.

High Volume Hiring
Enable rapid hiring process for quickly hire your workforce for rapid growth by sourcing candidates across multiple channels and screening them automatically

Diversity Hiring
Hire people based on skills while removing human bias to improve your diversity hiring efforts.

Sales Recruiting
Built a robust sales hiring engine for direct impact on your revenue topline with automated behavioral interviews.
Fully Integrated At Every Step
We offer 50+ integrations with job-boards, assessments,
communication tools & background verification providers
Globally Compliant and
Deployed Across Countries
A tool to handle even the complex non-linear process
across multiple geographies.

ISO 27001

GDPR

SOC 2

EEO
What our Clients says
Learn why 1500+ leaders use TurboHire

Amey Y.
Associate-Human Possibilities51-1000 employees, Oil & Gas
“Turbohire has improved the interviewer experience and the candidate experience. The quality of hiring has seen a consistent rise, and we have reduced the dependency on recruitment consultants to a large extent. Our team members love the platform.”

Uma Maheshwari,
Head Innovation & Talent Acquisition1000+ employees, Hospitals and Health Care
“I liked the ease of use. Within 24 hours we were up and running on TurboHire. I especially liked the fact that its all in one place, from requisitions to posting on all job boards, including having employee referrals tracked, all in one place.”

Vishak Bharadwaj
Senior Vice President500+ employees, IT Services & IT Consulting
“Ability to centralize the resumes into one place and allowing rediscovery on top to it. Additionally, the entire workflow is helpful for stakeholder management in recruiting.”

Amit Kataria
CHRO500+ employees, IT Services & IT Consulting
“Turbo tool for all your recruitment requirements. We are entirely dependent on the tool. Use of excel sheet for tracking candidate details and interview are eliminated with the use of TurboHire. ”

Nirmal Gulati
Recruitment Lead1000+ employees,Telecommunications



























“TurboHire has helped us in automating the recruitment process from raising job requisition to sending offer letters to candidates”